Sheer Network Scale Offers Hope for Solving Related Challenges
Imagine the cybersecurity implications of a world in which hundreds of millions of people have a physical impairment that leaves them internet-connected.
Thanks to the “internet of things,” that scenario is fast becoming reality in the form of internet-connected hearing aids. But like so many aspects of the internet of things, such devices carry upsides as well as big, potential data breach downsides, according to Phil Reitinger, the chief executive of the Global Cyber Alliance. He formerly was the Department of Homeland Security’s top cybersecurity official as well as CISO for Sony.
In an opening keynote presentation Aug. 2 at Information Security Media Group’s Fraud & Breach Prevention Summit New York, Reitinger noted that unlike some internet of things devices – toasters come to mind – internet-connected hearing aids, which are still in their infancy, offer a lot of promise for improving users’ quality of life. When a user is watching a television show, for example, their hearing aids could identify the audio and instead of amplifying it, begin downloading a live audio stream of the broadcast.
But what happens when internet-enabled hearing aids enter the workplace? As with smartphones, the devices would be a natural target for attackers, because they could be exploited and used to facilitate remote surveillance, allowing hackers to “hear” whatever the wearer hears. And that would create risks for any such device wearer who works for an organization with access to classified or sensitive information.
Without appropriate safeguards being put in place, Reitinger claimed we risk a future in which attackers could perpetrate targeted breaches with little risk of their attacks being spotted or traced.
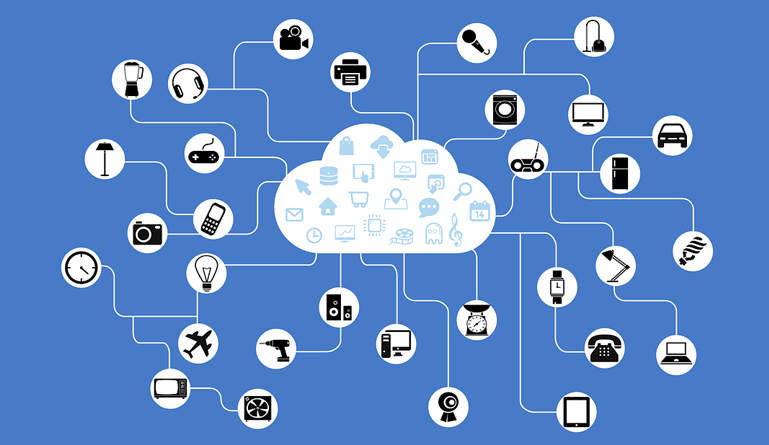
In that sort of a future, “things like the DNC [Democratic National Committee] hack, those are small potatoes … because a huge number of people are walking listening devices,” Reitinger said. “Everything is connected, everything is tied together.”
Click here to read more.
SOURCE: Bank Info Security
Mathew J. Schwartz





Leave a Reply
You must be logged in to post a comment.